by Jéssica Méndez Lema and Daniel Pérez Cabo – Alice Biometrics
EU citizens only need to take a selfie and capture an image of their government-issued identification (identity card, passport, driver’s license, etc.) to verify their identities online and access public services. If the system finds a match between the selfie and the person on the identity document, the user is verified and can access the service. Pretty simple, huh? But what is behind all this process? If you are wondering about the technology behind it, read on.
Context: Identity verification
Before we dive into the technology, it is important to put in context why EU citizens need to verify
their identity in public service online processes.
Traditionally, new users of public services need to provide their identity documentation so that the entity can confirm that they are who they say they are, as well as that they are using their own documentation. In today’s digitised world, companies and institutions need to onboard new users through remote digital channels. Therefore, the EU public administration needs a robust method to verify the identity of citizens operating online, not only to digitally authenticate identities, but also to detect any type of fraud that may occur, such as identity theft or forgery of documents.
But, what are the technologies that allow the verification of identities and documents? In other
words, what is the technology behind the identity verification of EU citizens in the online processes of public services?
Technologies involved in the identity verification solution
A digital identity verification solution is a combination of different technologies, based on Artificial Intelligence systems composed by Machine Learning algorithms:
- Facial recognition
- Liveness detection
- OCR
- Forensics analysis
Separately, these technologies can serve other purposes. But when it comes to building an identity verification solution to onboard users remotely, they all share one purpose: defeat fraud.
Let’s delve into each one before understanding the whole.
Facial recognition
Facial recognition is the biometric technology that focuses on recognising individuals based on their facial characteristics, distinguishing one individual from another. It answers the question: “whose face is this?”
When digitally verifying someone’s face, the facial recognition system needs to confirm that the
person taking the selfie is the owner of the identity document provided. In order to do so, it needs data from at least two different information sources.
In the identity verification of EU citizens, these two different sources of information are: a selfie and the photo of the identity document. The system scans these two sources and translates their information into numerical expressions that will be used to validate the identity.
Liveness detection
Liveness detection is the technology in charge of detecting if there is a real person behind a process involving facial recognition. Its objective is to confirm that a human being is carrying out an action, which avoids fraudulent practices, such as presentation attack detections (printed selfie, mask, etc.) or deep fakes for instance.
There are two types of life detection: active and passive. As the name implies, active life detection requires the user to perform a gesture, action, etc. On the other hand, the passive does not need any type of collaboration on the part of the user.
When it comes to verifying identities remotely, liveness detection is needed in order to secure
biometric authentication. Otherwise, fraudsters could cheat on systems using photos, videos, masks, etc. to access online services.
OCR
OCR, which stands for Optical Character Recognition, extracts printed text on the identity
documentation and converts it to digital format. Therefore, it is another key technology in digital identity verification since it makes the whole authentication process faster as it prevents typing errors and saves time.
But most importantly, this machine-encoded text helps to validate data against verification sources, which helps to validate names, addresses, identification numbers, etc. are real.
Forensics analysis
Last but not least, forensics analysis compounds the processes of reviewing, investigating, and
documenting the identity documentation provided by the user. Again, forensics analysis aims to
prevent fraud by detecting manipulation and edits in the documents.
Through AI-based, it adds an additional level of security by alerting in the event that the user uses a false or invalid identity document.
All technologies to improve one solution
As you can see, each technology (facial recognition, liveness detection, OCR and forensics analysis) adds its own features and complements the other ones to create a secure solution, which is also frictionless for the user.
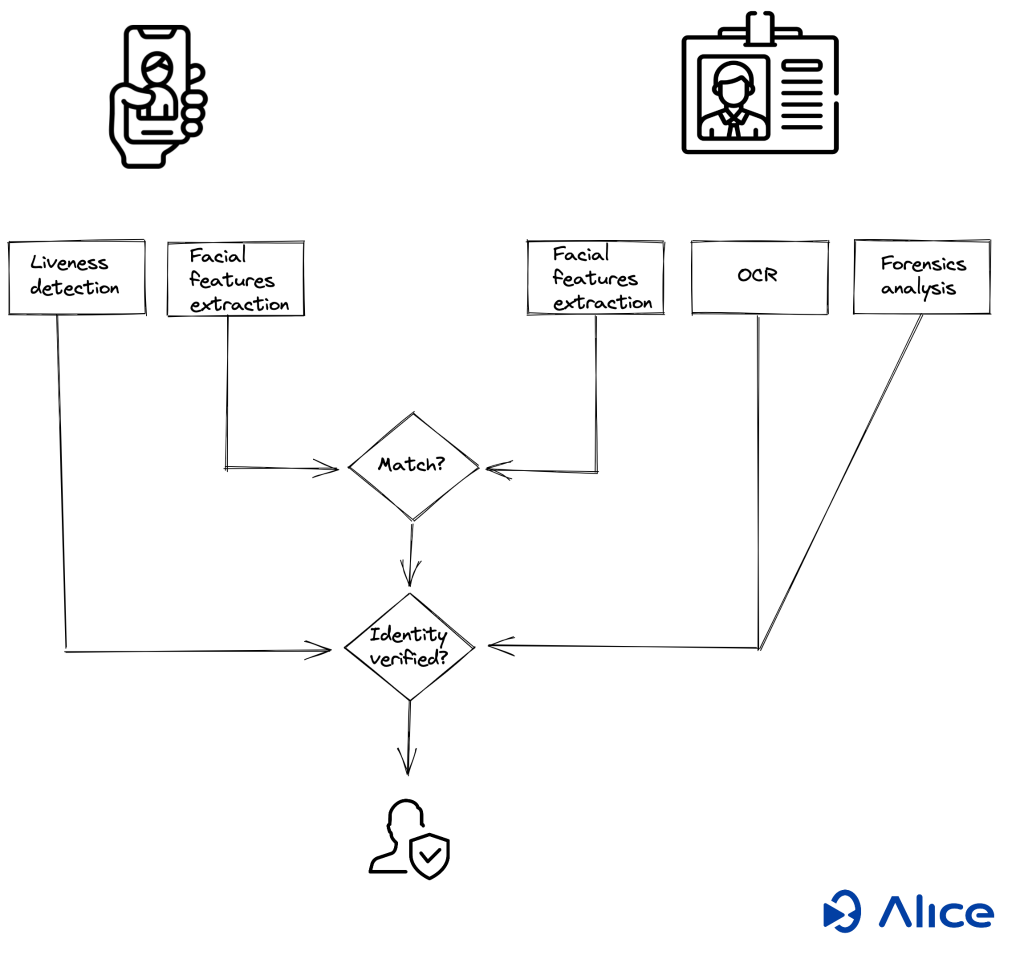
And how are they related during the process of verifying a user? The user just needs to take a selfie and capture a picture of their identity documentation.
But behind that selfie, there is an intelligent system (algorithms) previously trained to read the facial patterns of people’s faces and the face of the picture in the ID document. The gathered data, from the selfie and the picture, allows the facial recognition system to get a measure of similarity between the facial patterns in the selfie and in the picture of the identity document. Then, it makes a decision if there is a match belonging to the same identity or not.
Simultaneously, liveness detection also carries out an analysis of the user’s selfie in order to
determine if someone is performing an attack, like using a mask, a photo of a selfie, a photo of a
screen, etc.
On the other hand, when the user takes a photo of their identity document, the system extracts more than the picture, it also extracts the information, such as name, address, identification number, expiring date, etc. using an OCR system.
At the same time, the forensics analysis checks that there has been no editing or modification of any kind in the documents provided.
Definitely a winning combination: robust and secure technology for entities, and frictionless and easy to use for citizens.
At IMPULSE, identity verification runs on behalf of Alice Biometrics. Visit their website to learn more!
